Governed AI Security Operations Across Business Units and Customer Environments
AI agents provide scale for security operations teams to triage alerts, investigate threats, and execute other core workflows within the modern SOC. But most organizations run into the same problem the moment they try to deploy it beyond a single environment: governance breaks down.
Enterprise SOCs do not operate in a vacuum. They span business units, subsidiaries, and regulatory boundaries. Managed security providers operate across hundreds or thousands of customer environments. Each environment carries its own requirements for data isolation, access control, and operational independence.
AI introduces a new layer of complexity. It does not just process data. It acts on it. It moves across workflows, collaborates with many systems, and executes procedures that directly impact security outcomes.
Without clear boundaries, those capabilities create risk:
- data exposure across environments
- unauthorized actions
- lack of auditability
- breakdowns in compliance
To safely operationalize AI in the SOC, governance has to be built proactively into the architecture.
To support this, Bricklayer AI has introduced Multi-Organization & Service Provider Management, unveiled as part of its latest platform update at RSA. This capability enables enterprises and service providers to operate AI-driven security workflows across complex environments while maintaining strict control over data, access, and operations.
Enterprise Operations Across Business Units
Large enterprises rarely operate a single, unified SOC. Business units and subsidiaries often have distinct tooling, processes, and regulatory obligations. In practice, this creates multiple operational environments that must remain independent, even when they are part of a broader security program.
Multi-Organization Management reflects that reality.
Enterprises can provision structured sub-organizations beneath a parent environment, giving each business unit its own operational boundary. Data, workflows, and access controls remain isolated within each sub-organization, while the parent organization maintains centralized governance and visibility.
This allows enterprises to align security operations with how the business actually functions:
- Enterprises share best practices amongst workflows with procedure and integration templates
- Each business unit can customize independently with its own data and workflows
- Access is controlled at the organizational level through role-based permissions
- Visibility across environments is intentional and governed, not implicit
- Central teams retain oversight without breaking isolation boundaries
The result is a model where decentralization and governance are not in conflict. Each environment operates on its own terms while still aligning to a unified enterprise security strategy.
Service Provider Operations at Scale
For managed security providers, the challenge is similar.
Every customer environment must remain strictly isolated. At the same time, providers need centralized visibility, management, and control to operate efficiently across their customer base.
Service Provider Management enables this balance.
Providers can manage large numbers of customer environments within a single platform, with each customer operating as a fully isolated organization. AI-driven workflows, investigations, and procedures execute within the correct tenant boundary, ensuring that data and operations never cross environments.
At the same time, providers retain the ability to oversee operations across all customers from a centralized control plane.
This allows providers to scale without compromising trust:
- Best practices can be enforced by managing procedure and agent templates
- Each customer environment remains logically and operationally separate
- Workflows and procedures can be tailored per customer
- AI-driven investigations execute within the correct context
- Operational visibility is centralized without breaking tenant isolation
The outcome is operational scale with enforced governance.
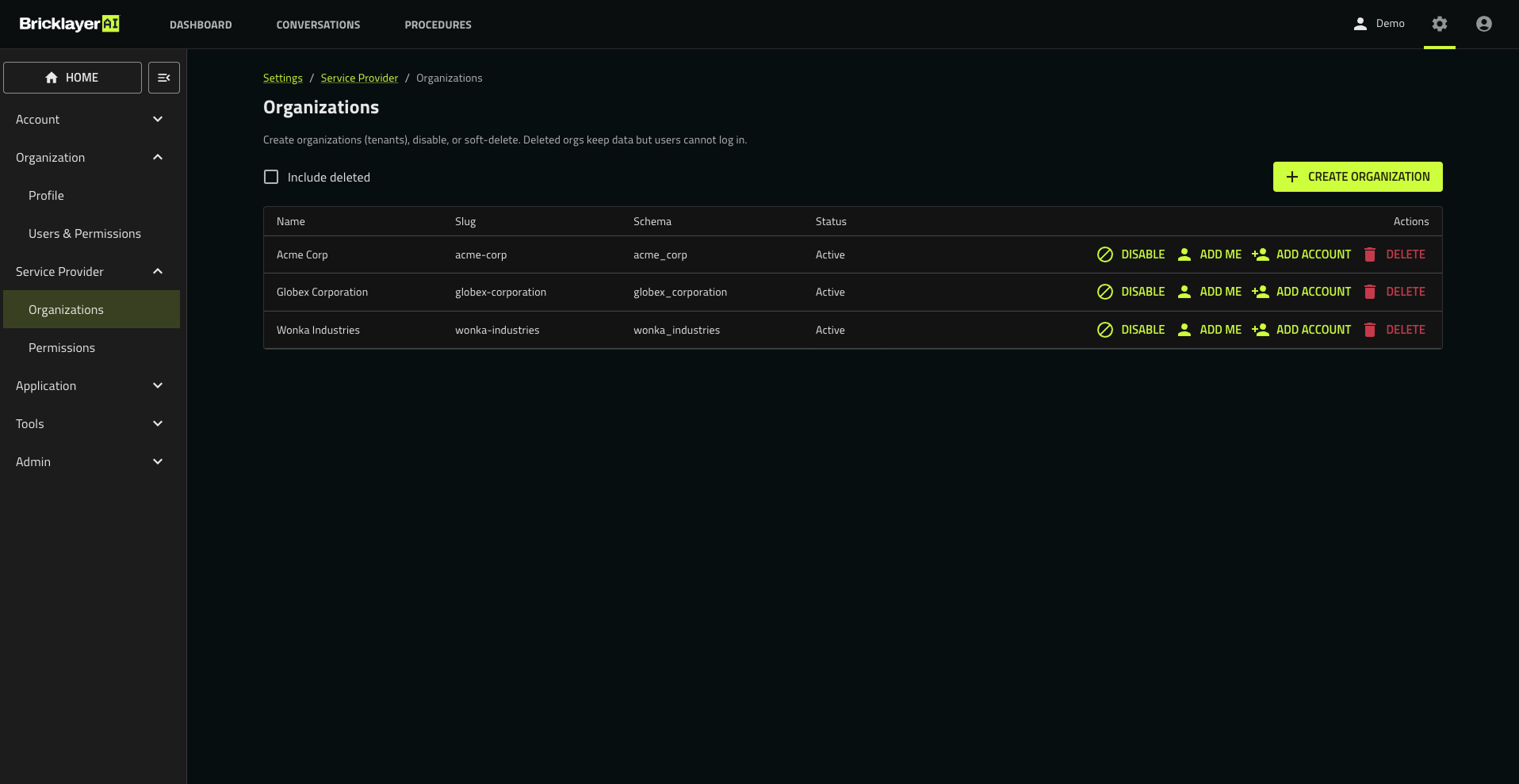
Creation of new customer environments within an MSSP for logical and operational separation.
Controlled Testing and Operational Change
Introducing AI into security operations requires more than deployment. It requires discipline.
New workflows, procedures, and automation must be tested, validated, and introduced without disrupting live operations. Multi-organization provisioning supports this by enabling structured environments for development, staging, and production within the same platform.
Teams can test workflows in isolation, measure outcomes, and validate changes before promoting them into production environments.
Organizations can also implement blue-green deployment strategies by running parallel production environments to validate new automation before shifting operational traffic. This reduces risk while allowing continuous improvement.
AI-driven operations can evolve, but within a controlled and methodical process.
Data Isolation by Design
Structural boundaries define how environments are organized. Schema-level data isolation ensures those boundaries are enforced.
Each organization and sub-organization operates within its own logical data environment. Data is never co-mingled across environments. Queries, investigations, and automated workflows execute strictly within the defined organizational context.
This ensures that:
- AI systems operate only on authorized data
- Investigations remain scoped to the correct environment
- Audit boundaries are clearly defined
Sensitive information is further protected through multiple layers of encryption, including encryption at rest, column-level protection for sensitive fields, and dedicated encryption keys assigned per organization or schema.
Customer-Controlled Encryption Keys
For organizations operating in highly regulated environments, control over encryption is not optional.
Bricklayer supports per-organization encryption keys and optionally AWS KMS-based key management to maintain external control of sensitive data with external hardware security modules.
By doing so, customers can retain control over:
- key lifecycle management
- rotation policies
- Auditing
This separation between platform operations and encryption control enables organizations to meet strict compliance and governance requirements without compromising operational flexibility.
Access Control and Auditability
Access control in enterprise and service provider environments is rarely simple. Different teams require different levels of visibility and control. Bricklayer is designed to support this complexity.
Role-based access control now extends beyond predefined roles, allowing organizations to create and manage custom roles that align to their operating model. Permissions can be set at a detailed level across organizations, data, and workflows. Users and teams only get the access they need. It allows organizations to enforce separation of duties, delegate control safely, and adapt access models as their operations evolve.
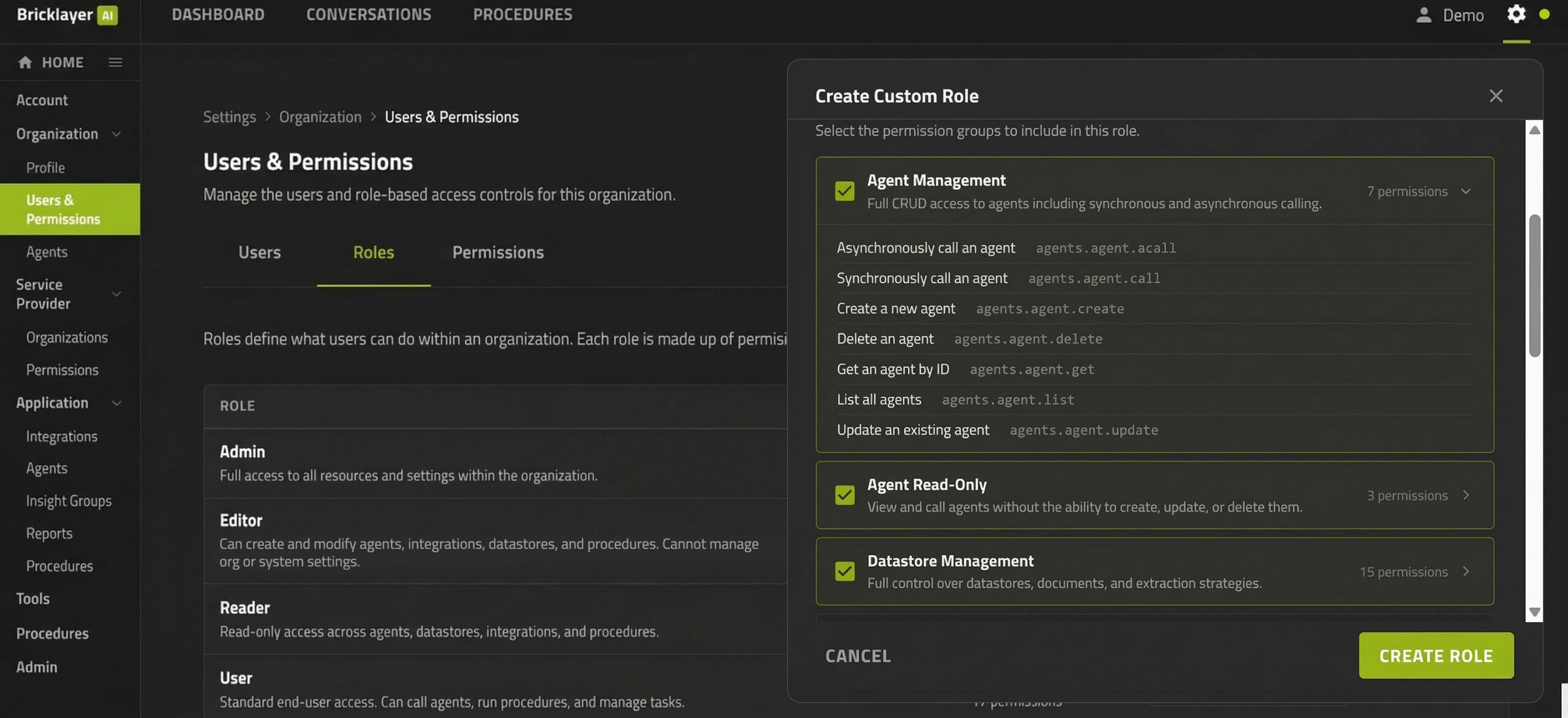
Enforce least-privilege access across agents, data, and operational workflows.
Control does not stop at access. Every action within the platform is recorded with full context, creating a complete and traceable history of how the system is configured and operated over time.
This level of auditability enables organizations to:
- Understand how workflows and automation evolve over time
- Trace operational decisions back to specific users or system actions
- Support internal reviews, compliance requirements, and external audits
Together, extensible access control and comprehensive auditability ensure that AI-driven operations remain transparent, accountable, and aligned with enterprise governance standards. This creates full transparency and trust into how the system operates over time.
For organizations that require independent retention or oversight, logs can be exported to a customer-controlled Amazon S3 bucket for long-term storage and compliance review.
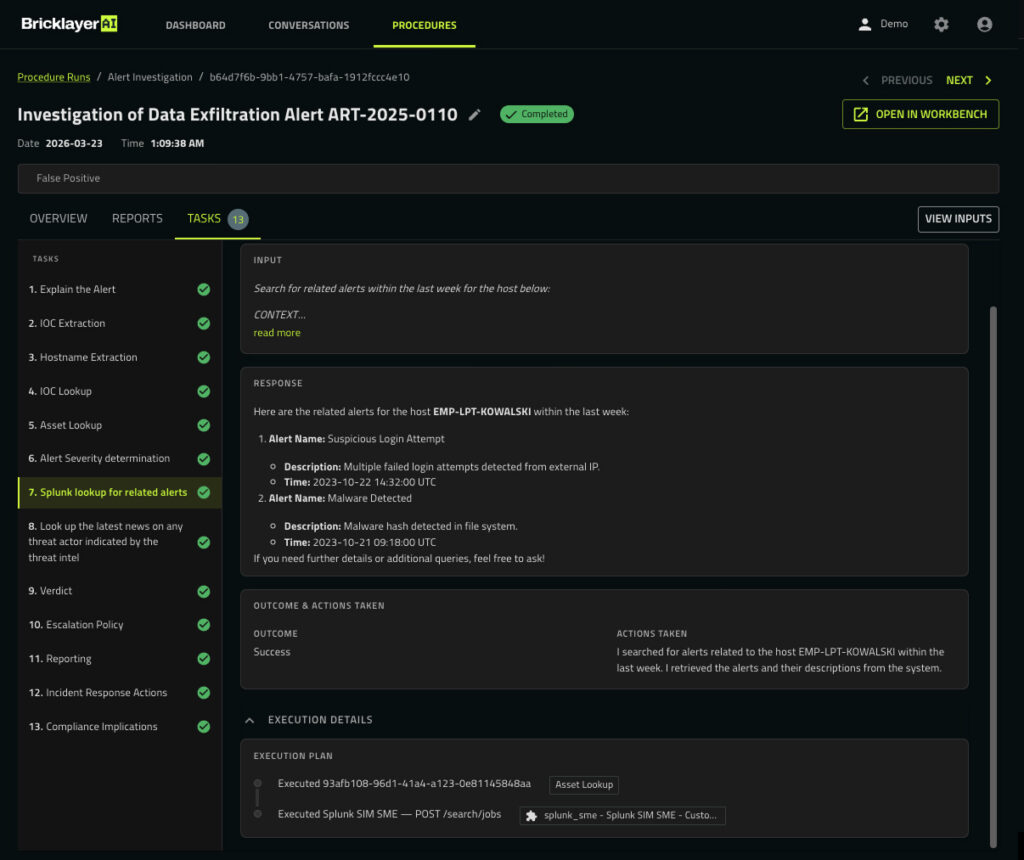
Every action within the Bricklayer platform is auditable. For every task run by a Bricklayer agent, an execution plan details the operation.
Governance for Enterprise and MSSP Environments
Multi-Organization & Service Provider Management is built on four foundational layers:
- Structural isolation between environments
- Data isolation enforced within the platform architecture
- Controlled access through role-based permissions
- Full auditability across configuration and operations
Together, these layers help towards AI-driven security operations remaining governed, observable, and compliant regardless of scale or complexity.
Governance is not a static requirement. As organizations inevitably expand their use of AI in the SOC, the expectations around control, transparency, and compliance will continue to evolve. Bricklayer is continuously expanding its platform to meet these demands, including new granted patents and ongoing investment in governance and security.
For organizations with the most stringent requirements, Bricklayer also supports a private cloud deployment model, extending control into fully isolated environments.
Enterprise Example
A global enterprise operating across eight subsidiaries can provision eight sub-organizations within a single parent environment.
Each subsidiary maintains its own isolated data environment, including schema-level separation and dedicated encryption keys. Security workflows, detection logic, and AI-driven investigations are configured independently to meet subsidiary-specific regulatory requirements and SOC operating procedures.
Access is scoped so that each subsidiary’s Org Admins and analysts can only operate within their own environment, while the parent organization retains Super Admin visibility across all subsidiaries.
All workflow changes, investigation activity, and configuration updates are logged and auditable at both the subsidiary and global level.
This allows each business unit to operate independently while maintaining strict data separation, controlled access, and centralized governance across the enterprise.
MSSP Example
An MSSP managing 200 customer environments can provision 200 fully isolated organizations within the platform.
Each customer environment has its own data boundary, workflows, and AI agent configurations. Investigations, alert triage, and automated procedures execute strictly within the assigned customer tenant, ensuring no cross-customer data access or operational overlap.
The provider can deploy customized workflows and procedures per customer while maintaining a centralized operational view across all accounts. The provider can also capture best practices through standardized procedures at the MSSP level.
Audit logs can be retained and exported per customer to meet individual compliance requirements, with full visibility into workflow changes, user activity, and investigation history.
This allows the provider to scale operations across hundreds of customers while maintaining strict tenant isolation, auditability, and customer-specific control.
The Next Phase of the AI SOC
AI will play a central role in how SOC teams operate. But adoption will not be driven by capability alone.
It will be driven by control.
Security teams will only deploy AI when it operates within the boundaries, permissions, and audit requirements as their environment.
Multi-Organization & Service Provider Management extends Bricklayer’s platform control, enabling AI-driven security operations to scale across enterprises and service providers with governance top of mind.
Scaling the SOC with AI is not just an automation problem.
It is a governance problem, and one that must be solved at the architectural level. Not reactively at the prompt level.
If you have been looking to scale your SOC operations with AI agents, but have been held back by security and governance concerns, schedule a demo to see how this works in practice.
